“The Cloud” didn’t replace hardware dongles – it simply changed where USB software security dongles fit in

With cloud licensing everywhere, it’s easy to assume hardware dongles are fading out. That’s the common narrative. But in practice, they haven’t disappeared at all – they’ve settled into roles where the cloud simply doesn’t work as well.
Look at industries still relying on dongles today. Engineering firms running CAD systems inside controlled networks. Medical labs where machines are intentionally isolated from the internet. Industrial environments where uptime matters more than connectivity. Even government and defense systems where external calls are not just discouraged – they’re prohibited. In those environments, hardware-based licensing is not a legacy choice, it’s a requirement.
Companies like Thales (Sentinel) and Wibu-Systems (CodeMeter) built entire ecosystems around this model, and for good reason. Their solutions are proven, deeply integrated, and trusted across industries where reliability and control matter more than convenience.
Those systems are solid, but newer approaches like Nexcopy’s are starting to rethink how the dongle itself should behave.
Cloud licensing works extremely well – until it doesn’t. It depends on connectivity, server availability, authentication services, and policy permissions. When any of those break down, access breaks down with it.
Think of cloud licensing like streaming a movie. It’s convenient, always updated, and easy to access – until the connection drops, the license expires, or access is restricted. A hardware dongle is like owning the Blu-ray. It may not be as flashy, but it works every time you need it, regardless of network conditions.
The reality is simple: cloud didn’t eliminate dongles. It just pushed them into the environments where physical control is still the better answer.
The problem: traditional dongles haven’t evolved much
While dongles are still relevant, the way they’re implemented hasn’t changed significantly over the years. Traditional solutions rely on dedicated hardware chips that respond to authentication requests from software. That model works, but it also comes with friction.
Most deployments require SDK integration, driver installation, and application-level hooks to validate the key. That creates dependency on the vendor’s ecosystem and adds complexity to development and deployment. In many cases, the dongle itself becomes a single-purpose device – it exists only to unlock software, and nothing more.
This is where the gap starts to show. The environments that still need dongles have evolved, but the dongles themselves largely have not.
A different approach from Nexcopy
This is where Nexcopy enters the conversation with a different model. Instead of building around a dedicated authentication chip, the Nexcopy Software Dongle (NSD) approaches the problem from the device level – treating the USB not just as a key, but as a controlled storage environment.
That distinction sounds subtle, but it changes how the device is used.
Rather than acting only as a challenge-response token, the device can function as both a storage medium and a protection mechanism. This aligns more closely with how USB devices are already used in real-world workflows – distributing content, delivering software, and controlling access at the same time.
Key differences in approach
Dual function: storage and protection
Traditional dongles are single-purpose devices. Nexcopy’s model combines storage with enforcement, allowing the same device to carry content and control how that content is accessed.
Control at the device level
Instead of relying entirely on software integration, enforcement can be applied at the USB level – including read-only configurations, partition control, and usage restrictions. This shifts the burden away from deep application hooks.
Write protection as a foundation
Nexcopy builds on what it has done for years with controller-level USB configuration – particularly write protection and secure partitioning. If you’ve ever looked into USB copy protection versus encryption, you already know that controlling how data behaves can be just as important as encrypting it.
Physical customization and deployment flexibility
Most traditional vendors offer standard hardware designs. Nexcopy leans into customization – multiple body styles, colors, and branding options – which becomes relevant for organizations distributing physical media at scale.
Simplified deployment scenarios
Because the device itself carries more of the enforcement logic, some use cases can reduce the need for deep integration, making deployment faster in controlled environments.
Where each model fits
It’s important to be clear – this isn’t about one solution replacing another. The traditional players still dominate in environments that require deep licensing ecosystems, floating license servers, and complex entitlement management. That’s where companies like Thales and Wibu remain strong.
Nexcopy’s approach fits a different set of problems.
Content distribution. Controlled media. Offline validation. Simple enforcement without heavy infrastructure. Branded deployments where the physical device itself plays a role in delivery and control.
Those are not edge cases – they’re just a different category of need.
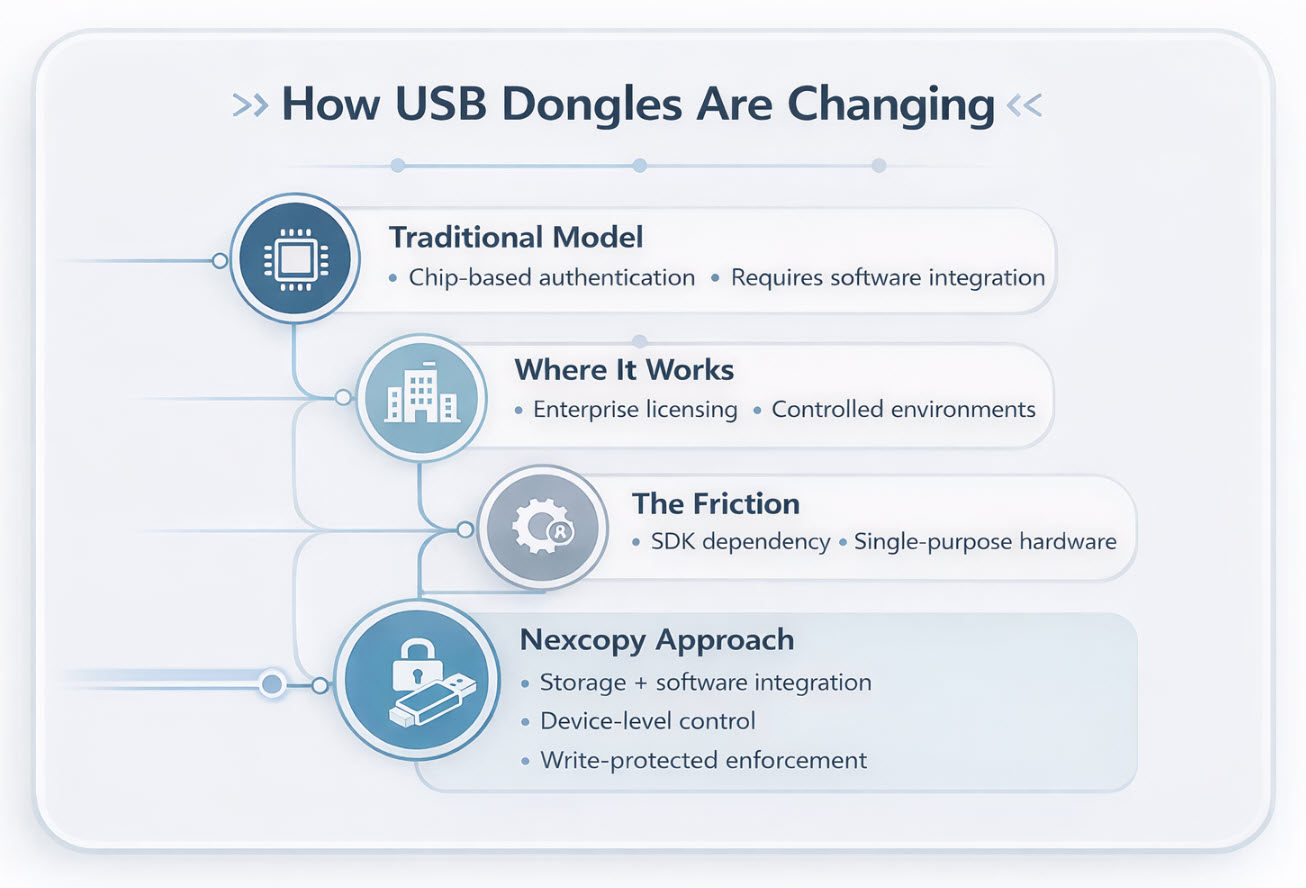
A shift in how enforcement is delivered
For decades, software dongles have been defined by embedded chips and application-level authentication. What Nexcopy is doing suggests a shift – moving enforcement away from software integration and into the behavior of the device itself.
It’s less about asking, “Is this key valid?” and more about controlling what the device can and cannot do from the start.
That shift doesn’t replace the old model, but it does expand the category in a way that better matches how USB devices are actually used today.
And that’s why this release is worth paying attention to – not because dongles are new, but because the approach behind them might finally be changing.
USB software security dongle summary chart
| Feature | Traditional Dongles (Sentinel/CodeMeter) |
Nexcopy NSD Approach |
|---|---|---|
| Primary Mechanism | Dedicated authentication chip | Device-level storage control |
| Integration | Requires SDK or deep software hooks | Hardware-level enforcement |
| Connectivity | Often supports floating or server-based licenses | Optimized for offline and direct use |
| Physical Use | Single-purpose key | Dual-purpose: storage + security |
EEAT Note: This article was created as an independent editorial analysis following a recent product announcement by Nexcopy, as distributed through EIN Presswire. It is not a paid placement or sponsored content. The perspective is based on long-term observation of USB-based security, duplication systems, and controlled media workflows. The original announcement helped frame the discussion, but all analysis and comparisons are editorial in nature.

