How To Copy Protect PDF Files
How to Copy Protect PDF Files Outside Adobe Ecosystem
This article will overview how to copy protect PDF files outside of the Adobe ecosystem. A couple of things worth mentioning before getting into the details:
- Encryption is different than copy protection. Encryption is a technology solution where the PDF owner assigns a password to the document and after the user enters that password the user can do anything they want with the file. Print, share, screen capture, etc. The idea for encryption is the document being unattainable until a password is entered.
- Copy protection does not use a password and anyone can see the file. However, the file cannot be copied, printed, shared or screen captured. The idea behind copy protection is the PDF being viewed by anyone, but nothing can be done with the file. When people are searching for PDF copy protection, this is the solution most likely sought after.
Challenges with PDF Security and Copy Protection
PDF or Portable Document Format is an open standard. What this means is the document format was designed to be used in just about any document reader program. The goal for the PDF specification was to make the format as universal as possible. For this reason, it is a bit more difficult than one would think to copy protect a PDF file.
Windows comes pre-installed with Adobe Reader. In addition, Windows has embedded Adobe API code to read PDF files. Even if Adobe Reader was not installed on your computer, or uninstalled, the underlying code is still there to open a PDF. In additional to Adobe Reader (#1 PDF reader in the market) there are dozens of additional PDF reader programs. Again, the goal for all these readers is to open and read a portable document file.
Adobe copy protection solutions are very well known for being cracked. If you Google “Adobe copy protection crack” you will find pages of ways the Adobe security features are compromised. Here and here are two examples of Google search results with web pages dedicated to hacking.
The fundamental problem with copy protection are the lack of controls when viewing a PDF. Meaning a PDF content owner (you) does not have the control over Adobe Reader, or other programs, to stop the user (your client/customer/student) from printing, screen grabbing, sharing and saving.
The idea behind a PDF copy protection solution is a framework where the PDF can be opened and viewed, while you (the content owner) maintains control of the document.
Of course Adobe Reader, FoxIt Reader and others, will not provide the tools to block a user from printing or saving from within their program. In contrast, we need a “reader” or “viewer” with controls to block those functions.
With this in mind, it is difficult to provide a reader with these security functions. Most users who receive a PDF do not want to download and install another program just to read a PDF file. The ease and beauty of a PDF gets lost in that process. No longer is the PDF a portable document format. In addition, a software program that can be downloaded to view a PDF can also be downloaded by a hacker to be reverse engineered. There needs to be something more than just a secure reader/viewer to control the PDF.
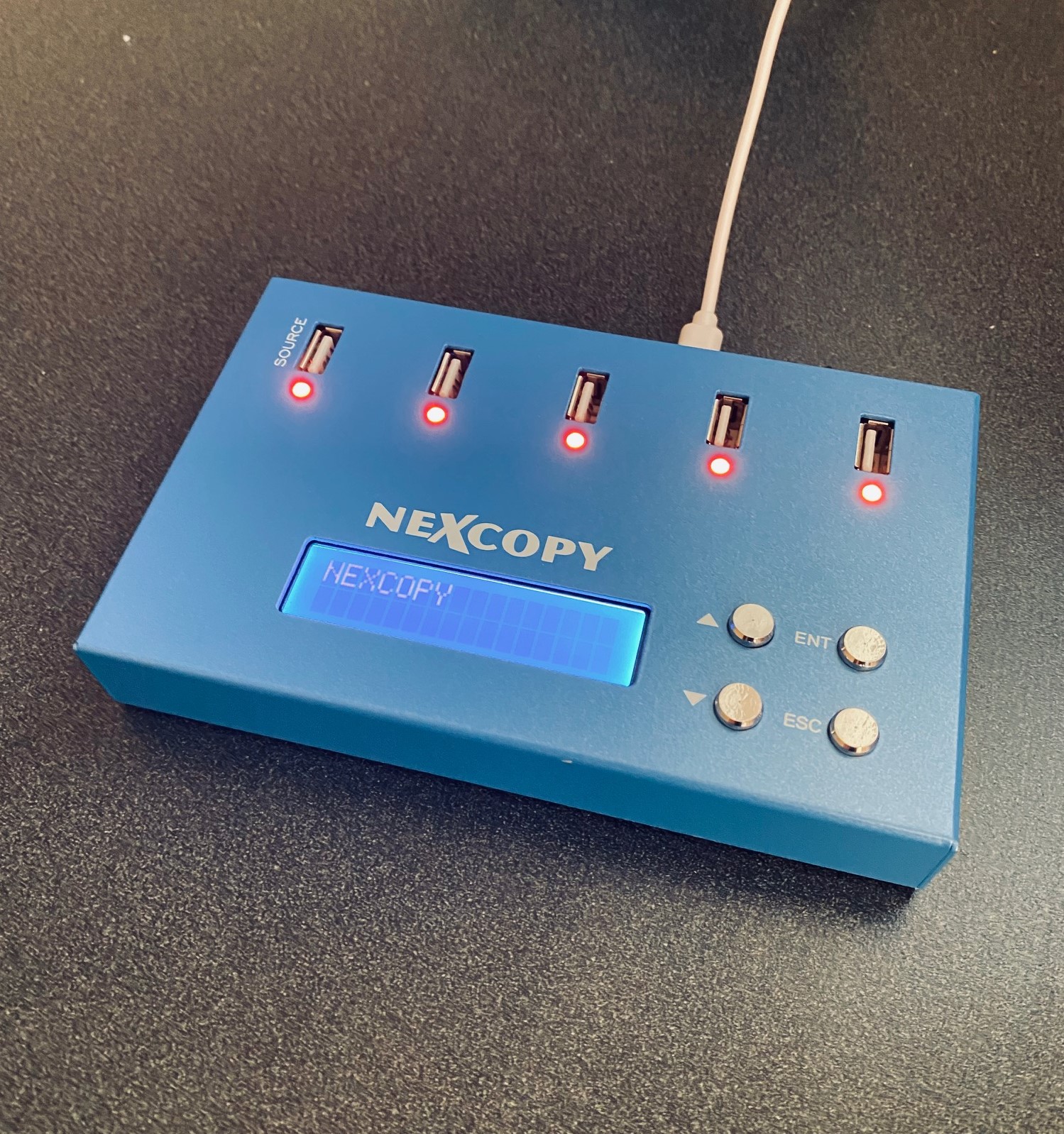
The most secure way to copy protect a PDF file is to associate it with something physical. There are some software (only) solutions, but those are not as secure as a solution with something physical.